Cloud Security Best Practices Every Developer Should Know in 2026
Security in the cloud is a shared responsibility — and the threat landscape has evolved significantly. From AI-assisted attacks to supply chain compromises and zero-trust architecture, here is what every developer needs to know to keep cloud infrastructure secure in 2026.
James Whitfield
Cloud Infrastructure Engineer · LightYear Cloud
Cloud providers secure the physical infrastructure — the data centres, the hypervisors, the network fabric. But everything above that layer is your responsibility: the operating system, your application, your data, and your access controls. This is the shared responsibility model, and understanding it is the first step to building secure cloud systems.
In 2026, the threat landscape has shifted considerably. Attackers are now using AI to accelerate reconnaissance, generate convincing phishing content, and automate vulnerability discovery at scale. Supply chain attacks — compromising a dependency or build tool to gain access to downstream systems — have become one of the most common and damaging attack vectors. And the perimeter-based security model has been definitively replaced by zero-trust architecture. Understanding these shifts is as important as the foundational controls.
Use SSH Keys, Not Passwords
Password-based SSH authentication remains a persistent source of breaches. Automated bots continuously scan the internet for exposed SSH ports and attempt credential stuffing attacks — and in 2026, these bots are faster and smarter than ever. The fix is straightforward: disable password authentication entirely and use SSH key pairs instead.
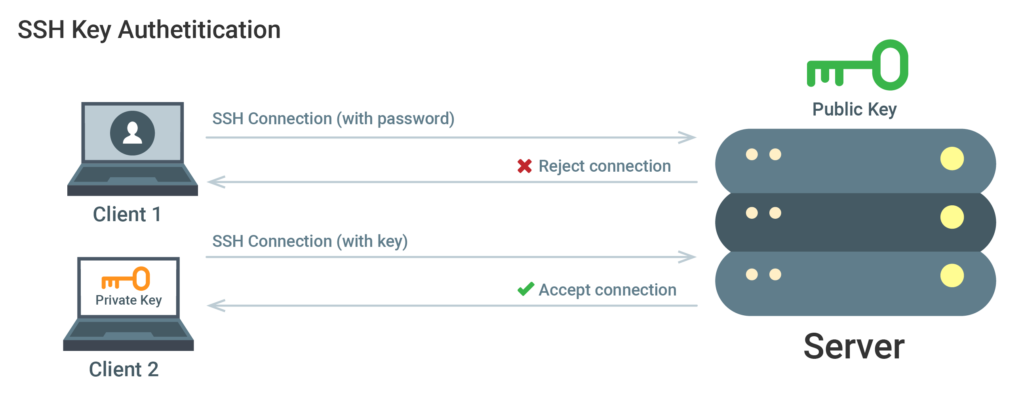
Generate a strong key pair (Ed25519 is the current recommendation), add your public key to the server, and disable PasswordAuthentication in /etc/ssh/sshd_config. This single change eliminates the vast majority of brute-force attack surface. For teams, consider using a bastion host or SSH certificate authority to centralise access management and enable short-lived credentials.
Apply the Principle of Least Privilege
Every user, service, and API key should have only the permissions it needs to perform its function — nothing more. This limits the blast radius of a compromised credential. Create dedicated service accounts for each application, use read-only credentials where writes are not needed, and audit permissions regularly.
Firewall rules follow the same principle. Block all inbound traffic by default and open only the ports your application explicitly requires. A web server typically needs ports 80 and 443. A database server should never be directly accessible from the public internet. Use private networking to connect services within the same infrastructure without exposing them externally.
Adopt a Zero-Trust Architecture
The traditional perimeter model — trust everything inside the network, block everything outside — is no longer adequate. Modern infrastructure is distributed across multiple clouds, regions, and edge locations. Zero-trust architecture replaces implicit trust with continuous verification: every request, from every user and every service, must be authenticated and authorised regardless of where it originates.
In practice, zero-trust means: strong identity verification for all users (MFA at minimum, hardware keys for privileged access), mutual TLS between services, short-lived credentials rather than long-lived API keys, and network micro-segmentation that prevents lateral movement if one service is compromised. These controls are no longer reserved for enterprises — the tooling has matured to the point where small teams can implement zero-trust principles without significant overhead.
Defend Against Supply Chain Attacks
Supply chain attacks — where an attacker compromises a dependency, build tool, or third-party service to gain access to downstream systems — have become one of the most damaging attack vectors in 2026. High-profile incidents have demonstrated that even well-resourced organisations can be compromised through a single malicious package or a hijacked CI/CD pipeline.
Practical defences include: pinning dependency versions and verifying checksums, using software composition analysis (SCA) tools to scan for known vulnerabilities in your dependency tree, signing build artifacts and verifying signatures before deployment, and auditing the permissions granted to third-party integrations. The principle of least privilege applies to your software supply chain just as much as to your infrastructure access controls.
AI-Assisted Attacks: What Has Changed in 2026
AI has lowered the barrier to entry for attackers significantly. Phishing emails are now indistinguishable from legitimate communications — AI generates them at scale, personalised to the target, with no spelling errors or awkward phrasing. Vulnerability scanning has been accelerated by AI-assisted tools that can identify exploitable misconfigurations faster than human security teams can remediate them.
The defensive response is to reduce the attack surface to the point where automated exploitation is difficult: eliminate unnecessary exposed services, enforce MFA universally, use anomaly detection to identify unusual access patterns, and treat every credential as potentially compromised. Security awareness training must also evolve — employees need to understand that AI-generated content cannot be trusted on appearance alone.
Keep Everything Updated
The majority of successful attacks exploit known vulnerabilities in unpatched software. Enable automatic security updates on your servers, subscribe to security advisories for the software you run, and establish a regular patching cadence for components that require manual updates. In 2026, the window between vulnerability disclosure and active exploitation has shrunk to hours in some cases — automated patching is no longer optional for internet-facing systems.
Enable Monitoring, Alerting, and Incident Response
You cannot defend what you cannot see. Set up logging for authentication events, firewall denials, and application errors. Configure alerts for anomalous patterns — failed login spikes, unusual outbound traffic, unexpected process launches, or access from unfamiliar geographic locations. Early detection dramatically reduces the impact of a security incident.
Equally important is having a documented incident response plan before you need it. Know who is responsible for what, how to isolate a compromised system without taking down dependent services, and how to communicate with users and stakeholders during an incident. Organisations that have rehearsed their incident response process recover faster and with less reputational damage than those that improvise under pressure.
Ready to experience reliable cloud hosting?
Deploy your first server in under 60 seconds. No contracts, pay only for what you use.
Get Started Free